April 2026
Overview
This release improves RDC-aware MCP setup and the change-password screen. Infrastructure and containers are hardened, and several security findings from scanning and testing are addressed.Improvements & new features
- RDC users and MCP — Your email is carried from the app through MCP authentication so RDC(Remote Data Center)-specific setup applies correctly. RDC users get MCP tools scoped per session, aligned with how you signed in.
- Change password screen — The change-password experience is restyled for clarity and consistency with the rest of the app.
Fixes and enhancements
These updates cover interface polish and behind-the-scenes reliability—grouped together because many fixes touch both what you see and how the service behaves.- Quick actions — Icons on quick-action buttons match the updated visual style.
- Display menu — The display menu layout is corrected so options line up as expected.
- Live streaming reliability — When the live event stream is briefly overloaded, the client retries in a controlled way so conversations recover instead of failing mid-reply.
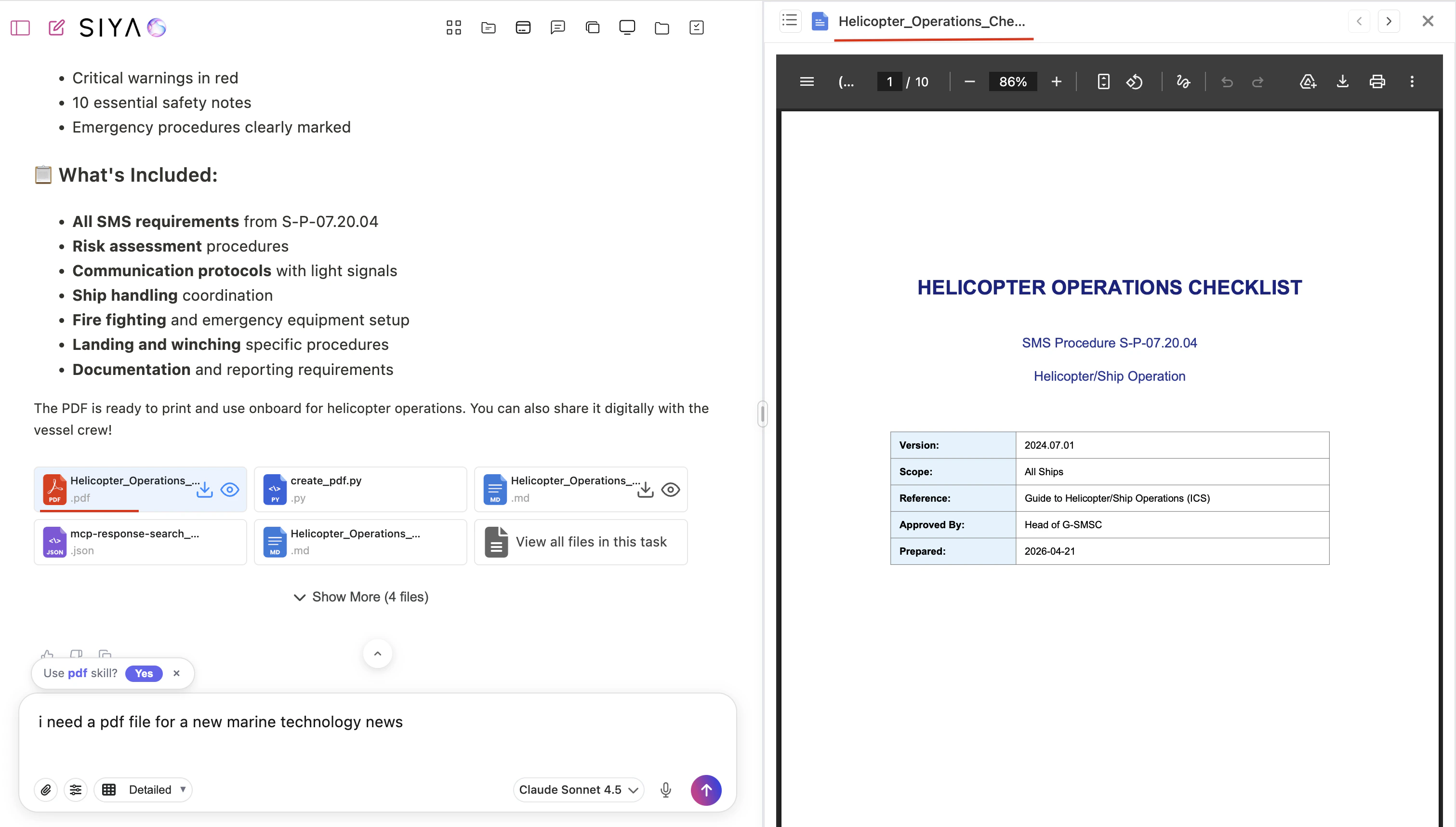
- PDF embedding checks — PDF links are no longer marked non-embeddable only because a quick check timed out.
- MCP tool data — A broad sweep of MCP environment data for redaction was removed so legitimate tool output is not blanked out by mistake.
- Guards and sub-agents — Security guardrails produce fewer false blocks on sub-agent work and outdated agent definitions.
- MCP OAuth errors — Error handling for MCP OAuth is better at matching the real failure so you see a useful message.
Security
- Kubernetes checks — All Checkov findings reported for our Kubernetes manifests are addressed.
- Least privilege in the cluster — A cluster-wide role is replaced with a namespace-scoped role where appropriate.
- Container hardening — The application user is no longer in the sudo group, reducing the risk of privilege escalation inside the image.
- Penetration test — A critical remote-code-execution issue found in testing is fixed.
- Browser-based coding environment — Allowed web origins are tightened, and the code-server instance uses password authentication.
- Image scanning — Trivy scans container images in CI/CD so vulnerable dependencies surface in the pipeline.
- Merge protection — Pull requests can be blocked when Trivy reports critical vulnerabilities in images.
- Shift-left on infrastructure — Kubernetes configuration is scanned with Checkov and Trivy as part of the PR workflow.
- Vulnerabilities and noise — Critical CVEs in dependencies are addressed, and Trivy rules are tuned so known false alarms on the Dockerfile do not block work unnecessarily.
